Zero Trust Security
Identity Access Management (IAM) forms the basis of a Zero Trust approach to cybersecurity. Traditional network perimeters are no longer effective in securing assets distributed across multiple clouds.
What is Zero Trust?
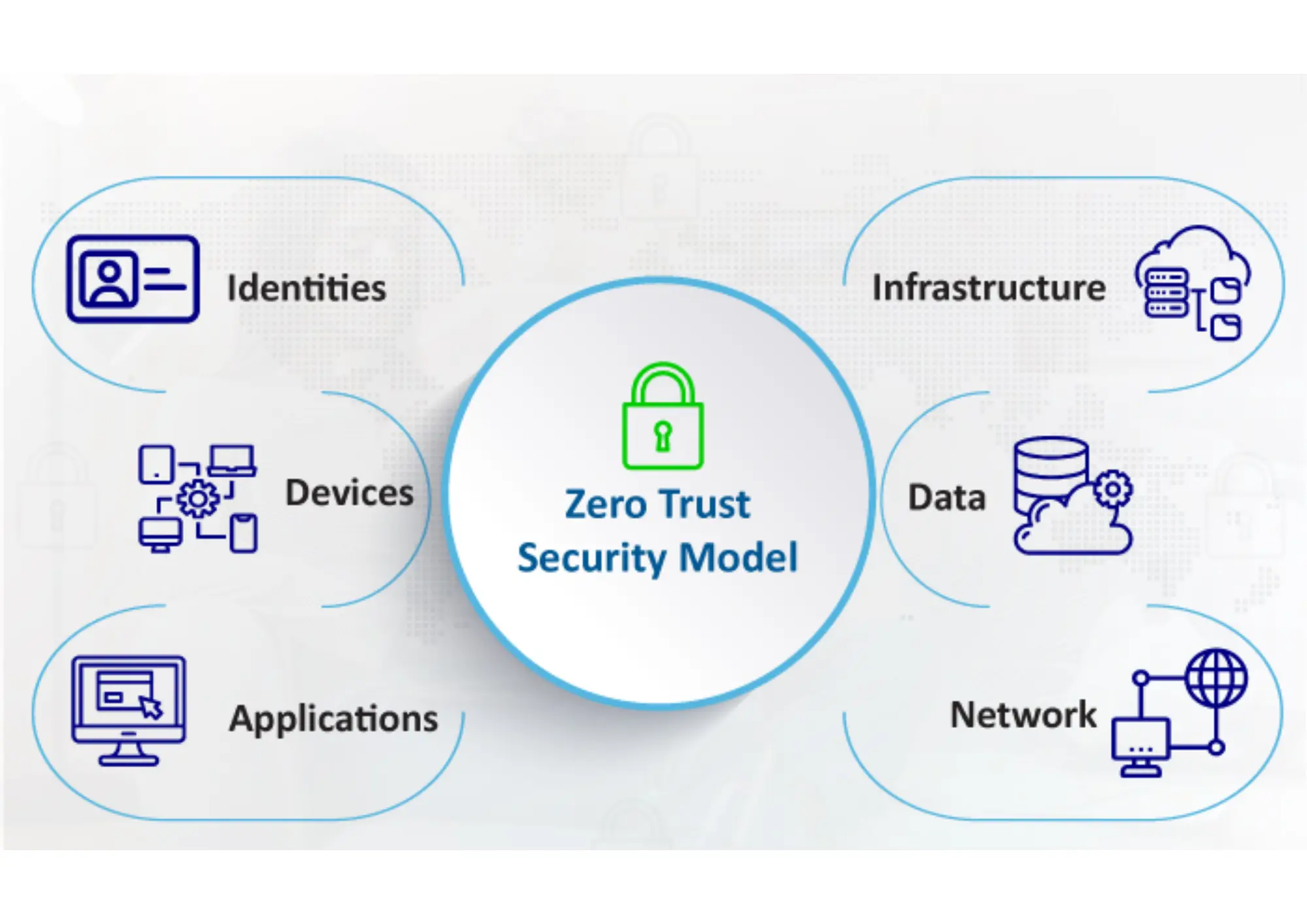
Identity Access Management (IAM) forms the basis of a Zero Trust approach to cybersecurity. Traditional network perimeters are no longer effective in securing assets distributed across multiple clouds. Digital Risk Management (DRM) and the shift to a Zero Trust approach move security from perimeter-based trust to identity-based trust.
A comprehensive Zero Trust architecture should include end users, applications, and services, and clearly define who can access what, when, where, and how. The goal is to verify identity before access is granted, reducing risks from hacking, ransomware, and lateral movement attacks.
With Zero Trust zone-protected perimeters, network attacks are reduced by allowing only authorized and verified users to access protected applications and services.
Security Outcomes
Stronger access governance, reduced attack surface, and consistent controls across distributed environments.
Why It Matters
Teams can modernize identity controls without slowing users, while maintaining privacy and compliance goals.
Seamless Platform Integrations
OKTA Integration
Zero Trust integrates with OKTA as a custom authenticator through the OKTA Devices SDK, helping organizations increase identity confidence while enabling secure access from any device across on-premise and cloud environments.
Zero Knowledge Proof
User identity attributes such as email, workplace credentials, location, and certifications can be verified through selective disclosure. Sensitive information is shared only when explicitly authorized by the user.